Unless you have been living in a cave over these last couple of weeks, you’ll probably have heard about the cyberattack that broke the internet for a few hours on several occasions. So what actually happened? It all starts with the DNS.
DNS stands for Domain Name System, in non-technical terms this is the technology that turns www.contradodigital.com into the servers IP address where your website files are hosted, for example, 178.238.139.113. There are many providers of DNS technology in use on the internet, with many providers using managed services of larger companies who have invested millions in the underlying hardware and infrastructure which enables the internet to work seamlessly. One of these companies providing DNS is called Dyn and here is where the cyberattack happened.
When the attack was happening, internet users in the following areas highlighted in the image below were unable to access many popular websites including websites like Twitter, SoundCloud, Spotify, Shopify and many more.
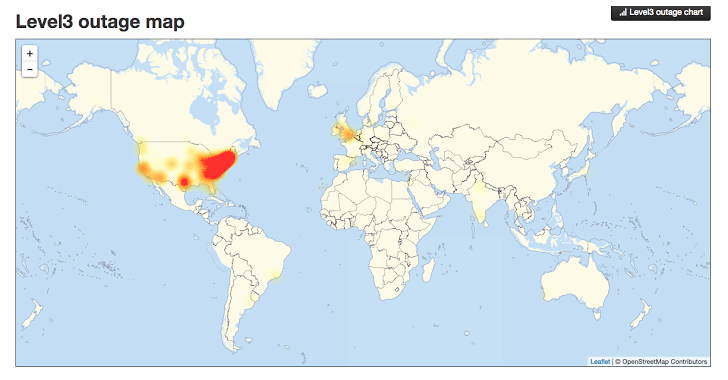
Image source: http://thehackernews.com/2016/10/dyn-dns-ddos.html
This is a significant part of the US and UK when customers and businesses could not access websites, meaning a significant drop in ecommerce sales for many organisations and a huge drop in productivity for those companies working in digital. For a system as large as the internet, which has been build with redundancy in mind, an attack of this scale is one of the worst we have seen to date and the seriousness of this means that businesses need to really step up in their cyber security efforts both large and small.
To read up more about the specifics of what a DDoS attack is and how this all happened, visit the Dyn website who have provided a write up on what happened.
Ultimately this attack was caused by hackers exploiting internet connected smart devices such as web cams and the likes. With the enormous rise in smart and internet connected devices available on the consumer market now, it is devices like this which are being exploited by hackers. When the software has been designed badly or built with un-updatable code or has been built with security holes in the code, it is this what is being exploited. Specifically using the Mirai software.
Distributed Denial of Service attacks are notoriously difficult to protect against, particularly on this scale with over 300,000 devices attacking a system. This is on the macro scale though and this really does just go to show that no matter how big you are attacks can happen to anyone. The even more worrying aspect is that this code has now been released open source so that the code is available to anyone wanting to exploit the same loophole.
The reality is that smaller and medium sized businesses are never reported on in the news. We deal with several hacked websites per month when businesses have failed to protect their self against cyberattacks. As a business owner you need to take cybersecurity seriously, and that means more than simply installing an antivirus and firewall on your laptops.
Picture this. You own a hotel. Imagine every door, windows, emergency exit and air vents into the building are ways of an attacker getting in. Not imagine your antivirus and firewall are your receptionists, blocking unwanted visitors in the building by locking the front door. Now imagine that all of the other doors, windows and vents in the entire building are left wide open for attackers to exploit. This is the reality that most businesses are dealing with without even realising. The software equivalent of this is that websites and web servers run outdated code, aren’t updated and active add security holes through using inefficient technologies and people to build systems. I cannot stress this enough, take cyber security seriously before you become the next victim. Sticking your head in the sand thinking that you will be fine will ultimately result in your business becoming the next headline. Be proactive.
Take advantage of our Free Digital Disaster Recovery Audit and test yourself on our Digital Evolution Score Card to see how advanced you are as an organisation and hence capable of dealing with problems. Better still, get in touch and we’ll talk you through the various options available for protecting your business, website and digital assets from cyberattacks.
Michael Cropper
Latest posts by Michael Cropper (see all)
- General Scheme of the Regulation of Artificial Intelligence Bill 2026 - February 4, 2026
- WGET for Windows - April 10, 2025
- How to Setup Your Local Development Environment for Java Using Apache NetBeans and Apache Tomcat - December 1, 2023
