A Short Story About… series, sharing stories about epic fails related to digital marketing, web design, technology choices and more. All designed to make you aware of what can happen when you work with the wrong people and an inexperienced digital agency. Remember the importance of working with the right digital agency.
Sharing these real life stories with you allows you to review your own setup to make sure you aren’t making the same rookie mistakes. Sharing is caring and it also makes our life easier when you speak with us about increasing your revenue through digital marketing and technology.
Look at our new shiny website!
The story starts here…. We received an email from a business owner who mentioned that they had passed on our details to another business owner related to some work that they needed support with. Nothing too strange here, we get this all the time.
Naturally, when we receive requests such as this, we have a quick nosey around to get a feel for the website, digital marketing channels, technologies in use and more. Based on this quick analysis we soon get a feel for where the business is at when it comes to how digitally advanced they are, or aren’t, as the case may be.
Having already heard of the business that had been referred to us, we already knew that the website was in development with another agency (sorry, we’re not going to name and shame here, but we shall say that they are local to us…). Based on this, we had a quick look around the new website;

Website X
Initial Investigations
One of the key areas we investigate is to see what technology the website has been built with and ultimately decide if we even want to get involved with helping the business. Depending on the technology used and other factors, we often turn down work that is just too far gone to help and there is no budget for a complete rebuild. Often bad decisions in the past can lead to costly solutions in the future, often which businesses don’t have budgets for re-doing something. Thankfully though, there is generally something we can help with in one way shape or form.
We always recommend the right solutions for businesses, it’s unfortunate that this ethos isn’t the same for all agencies, with many often using poorly configured technology, custom built technology and everything in between. Hence, why businesses come to us when things have gone wrong elsewhere and they are looking for a good solution that is truly suitable for their long term needs. As a caveat, there are a lot of good agencies around alongside ourselves and we can quite happily point you to them. It is also true, as many businesses are painfully aware, that there are a lot of charlatans around too.
So, while investigating what technology was powering the website, we soon noticed a login button on the website;
![]()
So we had a quick look at the login page to see if this resembled any of the common content management systems around;
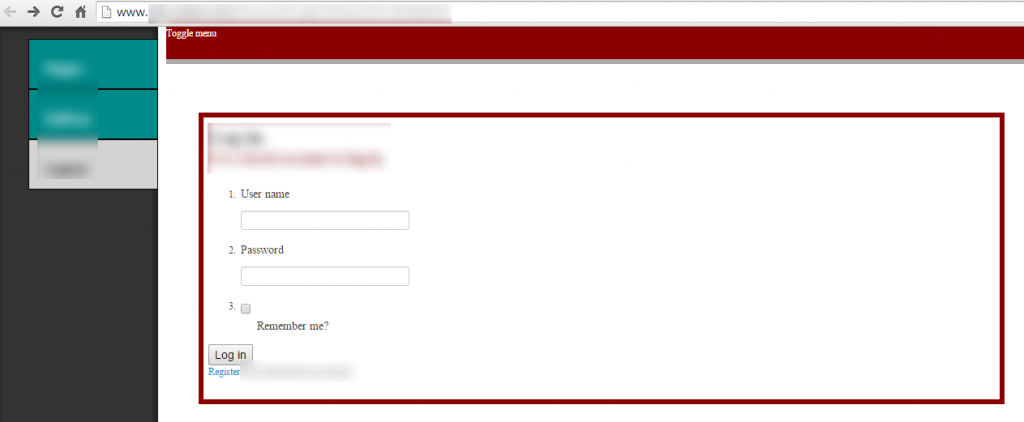
And what do we see here, a nice “Register” button, so we investigated a little further;

Ooohh, that looks like a nice easy registration form, so we tested a little further…;
- Username: test
- Password: test123
- Confirm password: test123
Surely any content management system or website worth it’s weight in salt would handle guest registrations in a graceful and secure way? Well, no, and this is where we were really shocked to see how bad this system has actually been built in terms of security. After registering a user using the form available on the website for anyone to see, we went back to the login page from earlier and tested these details;
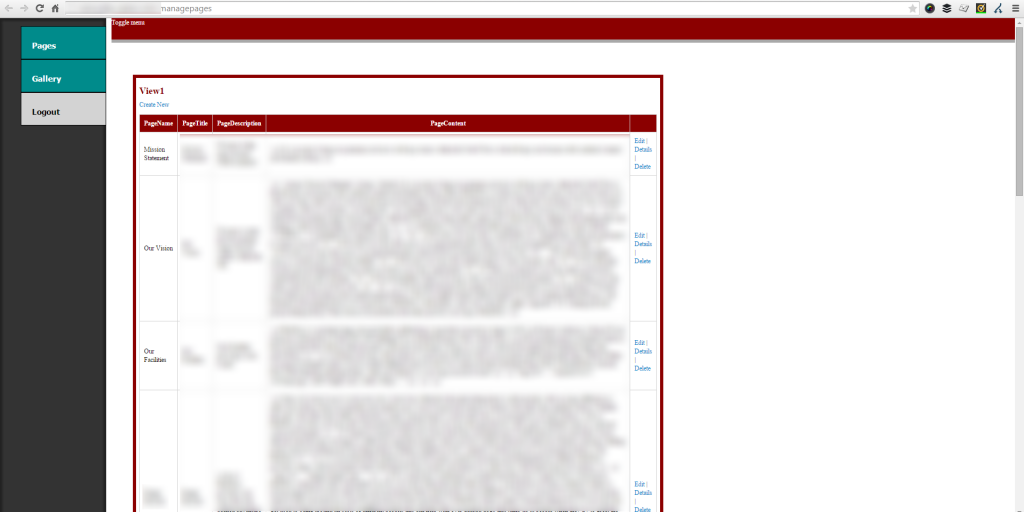
And here we are, straight into the administration area where we can edit the content of the website as we choose. Adding content, deleting content, uploading images in the gallery, addling links to websites of our choosing and more. To test that we do indeed have the right privileges, we added (and then immediately removed) a piece of content to the website which was visible once we updated this;
(Click for larger view)
The above isn’t the actual content that was added to the website for obvious reasons. It was simply a number “1” which was added to one of the sentences then removed immediately. The above image is purely for illustrative purposes and to emphasise the point.
It is extremely worrying that a website can be built with no security in place at all. This process took no more than 5 minutes to investigate, test and access the admin area. Imagine what we could do in 10 minutes…
Now if someone came along who had an axe to grind or was looking to infect websites with malware and other code, this would be extremely easy thing to do. Not only could this result in the website being blacklisted from Google, your own website visitors and customers could be infected with viruses or your website could be (unknowing to you) part of a bot net that is hacking many websites around the world.
This blog post is not designed to show how good we are when it comes to identifying security issues related to websites (although we aren’t too bad at that…), this blog post is designed to highlight how easy security issues can occur when you are using either the wrong technology, incorrectly configured technology, sloppy web developers or an agency who clearly has no idea what they are doing.
For any website or web application, security should be embedded from the start of the project and clear testing throughout to ensure that only those who have access to the administration area do have access to it. Security is not an added extra, this is your own business and website that we are talking about. An area that you have clearly worked hard on and one that will no doubt have been a reasonable investment. Don’t get caught out with rookie mistakes.
Imaging if the administration area contained a list of all of your customers who had registered with your website? Or if this contained personal sensitive information in unencrypted form, names, email addresses, phone numbers or heavens forbid credit card details? Such a simple mistake can turn into an enormous problem. All preventable when you are working with the right people who have the skills, knowledge and experience to do the job properly.
Technology
For reference, the technology behind the website in this case study was running the following;
- IIS 8 Web Server
- Net / ASP.Net MVC Framework (this is where the problem and solution lie, allowing anyone to view the user registration page and allowing the default user to be created as an Administrator)
- Google Hosted Libraries
- jQuery
- Fancybox
Incorrectly configuring technology is one of the most common pitfalls related to website security. It is so important that you are working with a well-respected company who have staff with a wealth of experience and capable of preventing issues like this occurring.
The Solution
Throughout this blog post, the company has remained masked and is not identifiable in any way for obvious reasons. The company has also been notified and their agency is working on a solution as a priority. We believe in responsible disclosure, which is why we have published these findings, to avoid others falling into the same trap.
For reference for the developers working on this solution, if any pointers are needed, a quick Google search for the solution came up which may be quite useful;
- http://stackoverflow.com/questions/12706236/restricting-access-to-register-user-in-asp-net-mvc
- http://forums.asp.net/t/1886372.aspx?How+to+remove+self+registration+from+mvc+4+Internet+application
- http://www.asp.net/web-pages/overview/security/16-adding-security-and-membership
- http://www.asp.net/mvc/overview/older-versions-1/nerddinner/secure-applications-using-authentication-and-authorization
- http://www.asp.net/mvc
Please also have some form of robust security processes in place within your business to prevent this happening again in the future. Please also check all of your other clients who you have built websites for in this same fashion, as this could also need fixing on their website too. Again, it is extremely simply to gather a list of websites built by the same agency where this problem could also exist;
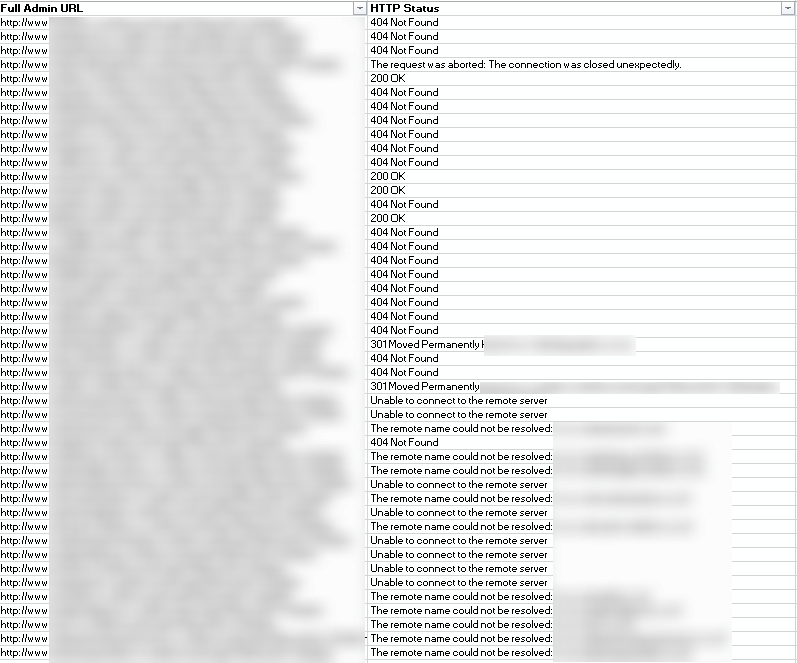
For anyone looking to do harm, this could turn into a reputational nightmare for the agency involved along with causing all of the businesses involved an awful lot of lost revenue if this was exploited fully by a hacker before a solution was implemented. Staff training, for both technical and non-technical users is key in this area to ensure that problems are identified before other people find them and exploit them.
Summary
As mentioned at the start, it is essential that you are working with the right digital agency who is capable of delivering projects in a secure fashion. Simply working with the cheapest company, the company who can talk the best talk or the company who manages to convince you that their solution is the best one over all of the others just isn’t going to cut it. As a business owner or decision maker, it is ultimately your responsibility that you are working with well-respected agencies who know what they are doing.
If you are concerned by the contents of this blog post, if you are questioning your current supplier or are generally concerned about the security of your digital assets, then get in touch. Cyber security is a hot topic for a reason, it is hugely important to protect the future of your online presence and more.
The learning point: Ensure your website registration process doesn’t allow new users to access parts of the website they shouldn’t. In this example, using a well-respected content management system would have prevented this issue altogether. Many website builds do not require any fancy custom built content management system solution, popular platforms such as WordPress or Magento are often perfect for the job.
Michael Cropper
Latest posts by Michael Cropper (see all)
- How to fix “Error establishing a database connection” on WordPress - May 19, 2026
- General Scheme of the Regulation of Artificial Intelligence Bill 2026 - February 4, 2026
- WGET for Windows - April 10, 2025