Well Tuesday was a fun evening watching someone relentlessly try and hack into the blog. Thankfully, they didn’t get in. Seriously though – why? Go & waste your time somewhere else instead of trying to actively cause harm. Anyway, I thought it was worth covering what this looks like on a WordPress blog and how it could quite easily have turned into a distributed denial of service attack (DDoS) due to the way it was being done. And I guess the most important bit, how you can prevent this type of attack on your WordPress blog with the help of a simple plugin, which thankfully I had installed already.
The Cool DDoS Hacking Attack Visualisation
While I’m sure all of the information in this post will be useful, by far the coolest bit is the fancy visualisation that I was able to create with some handy software. Feast your eyes on this;
The above video shows the attack trying different passwords/usernames on wp-login.php by attempting to force access by guessing the password. The video is just a small snapshot of the attack which was happening for almost 9 hours on and off, I guess someone had the afternoon off work then…
The Data
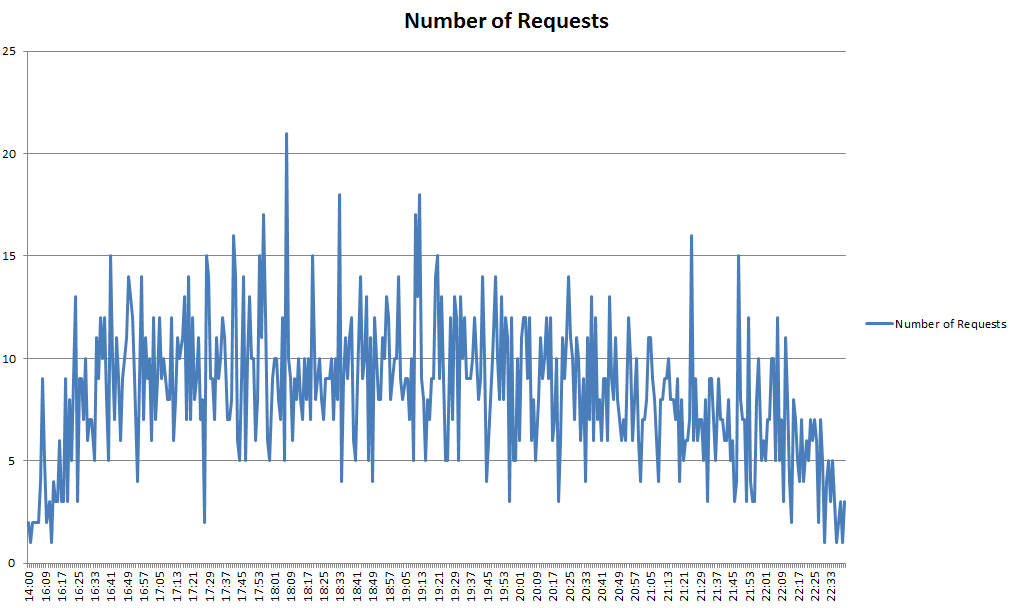
Being a bit of a data geek, I couldn’t resist the opportunity to dig into this a little deeper. Below shows the number of requests per minute between the time the attacks started to when they finally gave up.
(click for larger graphic)
While these figures aren’t enormous, when the blog isn’t on enterprise class hosting this can slow the website down and more than anything it is just a bit annoying.
Why A DDoS?
Why is this attack different than someone just simply attempting to guess a password? Well, this person is clearly well equipped with a bag full of IP addresses. I’ll explain about how to prevent your WordPress blog being hacked via this method a little later, but what I can say that if it wasn’t for the plugin that was installed, this could have been a lot worse.
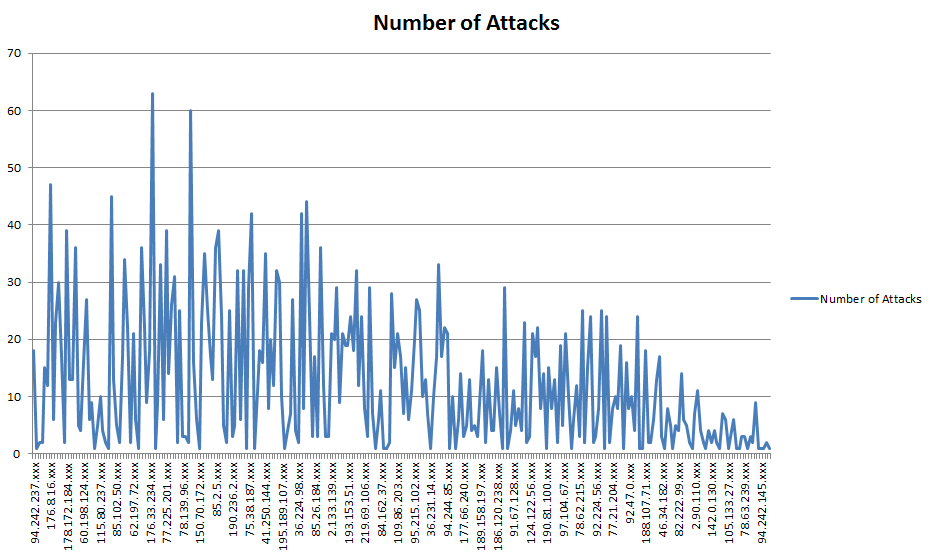
Another beautiful graph showing the number of attacks per IP address (this is only a selection);
(click for larger graphic)
I’ve not posted the IP addresses fully as, unlike the people doing this, this isn’t right as they could be hacked computers where these requests were coming from. In total there was 268 IP addresses used during the attack, which is quite considerable! The average number of attacks per IP address was at 12.38, which was no doubt limited by the plugin that was installed to stop people attempting this type of hacking attempt.
How to Prevent a DDoS Hacking Attack on Your WordPress Blog
Do you have a WordPress blog? Then I seriously suggest installing a plugin called “Limit Login Attempts”. What this plugin does is, well exactly as you an imagine, it limits the login attempts based on the users IP address. If someone guesses your login details incorrectly for 2, 4, 8, 12, whatever, number of times then the IP address will be blocked for a set period of time. This type of plugin can further block IP addresses longer term, all automatically, if the same IP address keeps coming back and trying again.
Had this plugin not been installed, I can’t imagine how many requests all 268 IP addresses would have tried during this period. While this was an interesting experience and has produced a cracking visualisation, I hope it doesn’t happen again either to me or anyone else.
Michael Cropper
Latest posts by Michael Cropper (see all)
- WGET for Windows - April 10, 2025
- How to Setup Your Local Development Environment for Java Using Apache NetBeans and Apache Tomcat - December 1, 2023
- MySQL Recursive Queries – MySQL While Loops – Fill Zero Sum Dates Between Dates - October 6, 2023